Late one evening, a systems engineer stared at a blinking cursor while tracing a strange spike in traffic. The logs were unremarkable until one identifier kept reappearing, quietly persistent among thousands of connections: 158.63.258.200. To most people, an IP address is just a string of numbers. To those who build and protect the digital world, it is a breadcrumb trail, a starting point for stories about infrastructure, intent, and identity.
In a networked economy where every transaction leaves a trace, understanding how to interpret an IP like 158.63.258.200 is no longer a niche technical skill. It sits at the intersection of cybersecurity, digital forensics, business intelligence, and trust. Whether you are a founder safeguarding your startup’s data, a developer debugging a system, or a tech reader curious about how the internet really works, decoding the meaning behind an IP address reveals far more than most expect.
What an IP Address Really Represents
An IP address functions as a digital locator. It helps devices identify one another across the internet’s vast mesh of networks. But unlike a street address, it is not static in meaning. It can point to a home router one day and a corporate cloud server the next, depending on allocation and usage.
At a technical level, an IP is part of the Internet Protocol, the rulebook that governs how packets move across networks. IPv4, the older and still widely used version, relies on numerical identifiers separated by dots. Each segment maps to a hierarchical structure that helps route traffic efficiently across regions and service providers.
Yet the true value of an address like 158.63.258.200 lies not in the numbers themselves but in the context surrounding them. Ownership, hosting environment, network reputation, and behavioral patterns all shape what that address signifies in practice.
Breaking Down 158.63.258.200 in Context
When analysts encounter an unfamiliar IP, they rarely look at it in isolation. Instead, they evaluate multiple dimensions that paint a broader picture of its role within the internet ecosystem. That includes geolocation, hosting provider, routing history, and historical activity patterns.
Below is a simplified overview of the kinds of attributes professionals typically evaluate when assessing an IP address.
| Attribute | What It Indicates | Why It Matters |
|---|---|---|
| Geolocation | Approximate region or country | Helps identify jurisdiction and routing patterns |
| ASN (Autonomous System Number) | Network owner or provider | Reveals infrastructure lineage |
| Hosting Type | Residential, corporate, or cloud | Signals likely usage patterns |
| Reputation Score | Historical behavior indicators | Important for security decisions |
| Reverse DNS | Domain linked to the IP | Adds contextual clues |
While the table provides structure, interpretation remains nuanced. For instance, geolocation is rarely exact and often reflects where a network is registered rather than where a user physically sits. Similarly, cloud-hosted addresses frequently shift between customers, complicating attribution.
The Role of IP Intelligence in Modern Business
For entrepreneurs and digital leaders, IP awareness has evolved from a backend concern into a strategic layer. The same identifier can serve multiple purposes across different functions within an organization.
In cybersecurity, IP monitoring forms the backbone of threat detection. Suspicious login attempts, distributed attacks, and credential stuffing campaigns often originate from clusters of identifiable addresses. Recognizing recurring IP patterns allows teams to respond faster and reduce risk exposure.
Marketing and analytics teams use IP data differently. By aggregating location insights, companies can personalize user experiences or identify geographic demand trends. Although privacy regulations limit granularity, aggregated IP intelligence still offers valuable directional insight.
Meanwhile, product teams leverage IP analysis to improve infrastructure performance. Traffic routing decisions, server placement, and latency optimization all benefit from understanding where requests originate and how they travel through networks.
When an IP Becomes a Signal
Not all IP addresses carry equal weight. Some pass quietly through logs without consequence. Others become signals that trigger deeper investigation. The difference often lies in repetition and behavior.
Consider how an address like 158.63.258.200 might appear in different scenarios. In one case, it could represent a benign user accessing a website through a corporate network. In another, it might be tied to automated scraping activity or a botnet node probing for vulnerabilities.
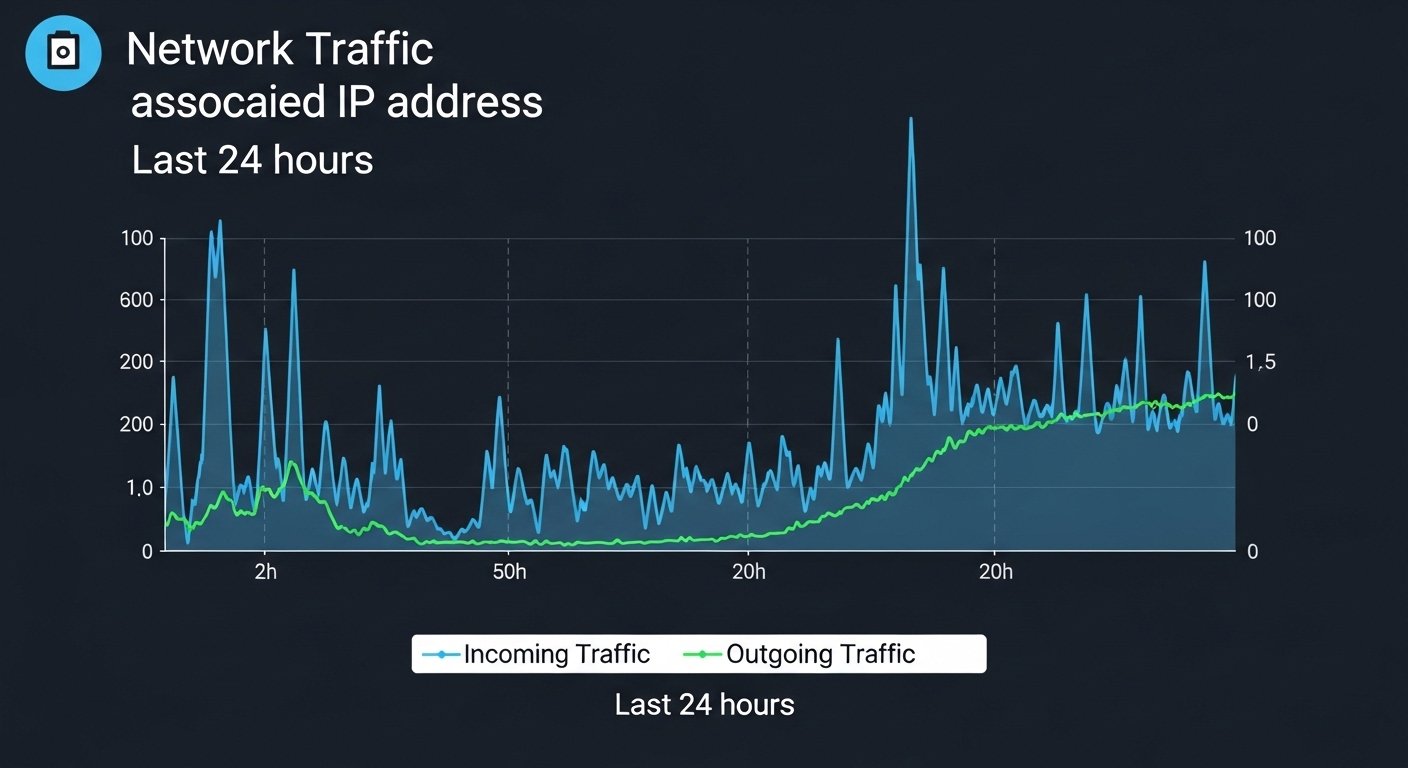
Professionals avoid jumping to conclusions based solely on a single data point. Instead, they look for correlation. Does the address appear across multiple failed login attempts? Is it associated with unusual traffic spikes? Does it match known threat intelligence feeds?
This pattern-based approach mirrors broader trends in digital decision-making. Data gains meaning when contextualized. A lone IP is rarely a verdict, but it can be the first clue in a much larger narrative.
The Cloud Effect on IP Attribution
The rise of cloud computing has fundamentally reshaped how IP addresses are interpreted. A decade ago, tracing an IP often led directly to a physical location or a specific organization. Today, the trail frequently ends at a shared cloud environment serving thousands of tenants.
This shift complicates attribution. An address might belong to a reputable cloud provider while still hosting malicious activity initiated by a temporary user. Conversely, blocking entire cloud ranges can disrupt legitimate traffic, creating a delicate balance between security and accessibility.
For founders building digital products, this reality introduces a new operational mindset. Security policies must adapt to ambiguity. Rather than relying solely on static blocklists, modern defenses incorporate behavioral analytics, adaptive filtering, and real-time monitoring.
Legal and Ethical Dimensions
IP analysis sits within a broader legal and ethical framework that continues to evolve. Regulations around data privacy, cross-border data flows, and digital surveillance shape how organizations can collect and interpret IP-related information.
In regions governed by strong privacy standards, IP addresses are treated as personal data. That classification imposes responsibilities around storage, processing, and disclosure. Companies operating globally must navigate these differences carefully, especially when building analytics pipelines or fraud detection systems.
Ethically, transparency matters just as much as compliance. Users increasingly expect clarity about how their data is used, even when that data appears technical or abstract. Communicating openly about IP logging and security practices builds trust in ways that technical measures alone cannot.
The Entrepreneur’s Perspective
For startups and scaling companies, the conversation around IP addresses often starts reactively. A suspicious spike in traffic, a flagged login pattern, or an unexpected downtime incident forces the issue into focus.
But forward-thinking founders treat network intelligence as a proactive asset. Integrating IP monitoring early can uncover insights that extend beyond security. For example, understanding where early adopters cluster geographically can inform expansion strategies or infrastructure planning.
There is also a reputational dimension. In an era where trust fuels growth, demonstrating robust network hygiene signals maturity. Investors and enterprise clients increasingly evaluate security posture as part of due diligence. Knowing how to interpret identifiers like 158.63.258.200 becomes part of a broader narrative about operational resilience.
From Numbers to Narratives
One of the most fascinating aspects of IP intelligence is how it transforms raw data into narrative. A single address can connect multiple layers of digital experience: infrastructure decisions, user behavior, geopolitical routing, and even economic patterns.
This storytelling dimension explains why IP analysis continues to attract attention beyond purely technical circles. Journalists investigating cyber incidents, policymakers debating digital sovereignty, and executives assessing risk all rely on the same foundational signals.
The challenge lies in resisting oversimplification. It is tempting to treat an IP address as a definitive identity marker. In reality, it functions more like a waypoint in a constantly shifting network landscape. Meaning emerges through aggregation, correlation, and interpretation.
Why Context Always Wins
If there is one lesson repeated across cybersecurity, analytics, and digital operations, it is this: context outweighs raw data. An address like 158.63.258.200 holds value not because of the numbers themselves but because of how those numbers interact with time, behavior, and infrastructure.
A spike in traffic at midnight carries a different implication than the same spike during peak hours. An IP tied to automated requests may be benign in one context and suspicious in another. Interpretation demands both technical literacy and situational awareness.
This emphasis on context mirrors a broader shift in the technology landscape. As data volumes explode, competitive advantage increasingly comes from interpretation rather than collection. The organizations that thrive are those that transform signals into insight.
The Future of IP Visibility
Looking ahead, the relevance of IP intelligence is unlikely to fade, even as technologies evolve. IPv6 adoption, edge computing, and decentralized architectures will introduce new layers of complexity, but the need for digital identifiers will remain.
What will change is how those identifiers are interpreted. Machine learning models already assist in anomaly detection, uncovering subtle patterns humans might miss. Privacy-enhancing technologies will reshape how data is anonymized and shared. Meanwhile, regulatory frameworks will continue to redefine boundaries around digital identity.
For professionals navigating this evolving landscape, adaptability is key. Understanding the fundamentals of how IP addresses function provides a durable foundation, even as the surrounding ecosystem shifts.
Conclusion
At first glance, 158.63.258.200 looks like a simple numerical label. Yet within that sequence lies a gateway into the deeper mechanics of the internet. It represents routing decisions made in milliseconds, infrastructure built over decades, and human behaviors unfolding across continents.
For entrepreneurs, technologists, and digital leaders, the lesson is clear. The smallest technical details often carry the largest strategic implications. Interpreting something as modest as an IP address can unlock insights about security posture, operational maturity, and digital trust.
In a world defined by invisible connections, understanding the meaning behind identifiers like 158.63.258.200 is not just a technical exercise. It is a window into how modern systems function and how organizations can navigate them with clarity and confidence.